During my summer project of investigating IT security and AI, I am having a hard time picking a topic to dive into. Especially when it comes to IT security, that is insanely big. From now on, I may question people with the title of IT security experts. Ask them which part of IT security, they are experts in, as they can’t possibly be export on it all.
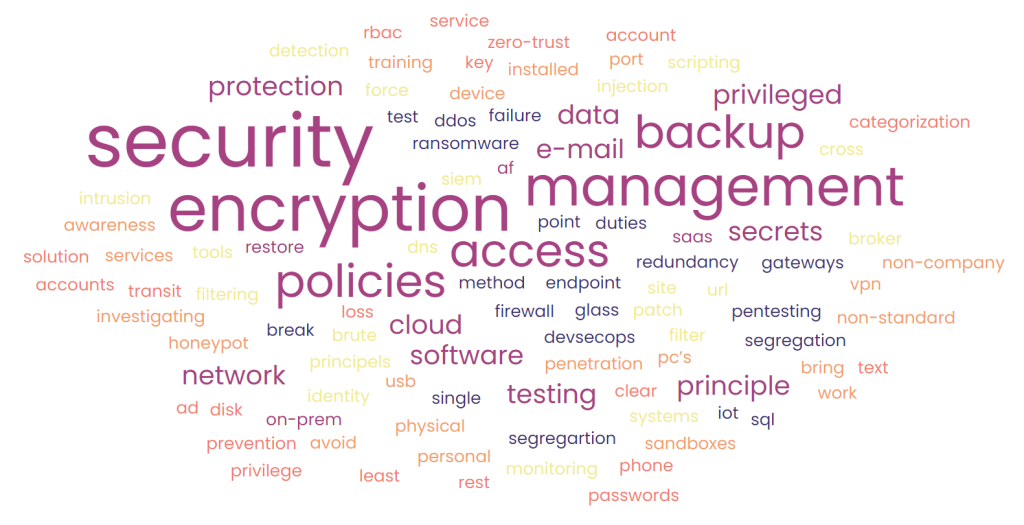
I decided to do a brainstorm of all the cyber security related topics, I could come up with. It led to the list below. 56 items, and some of them are huge just by themselves. Take least privi-lege access principle of users only having access to what they need and nothing more. The scary thing about this is imaging what it would require implementing and enforcing the whole list.
I guess what is important and often overlooked is to prioritize and be clear about what is left out of scope. It is a difficult exercise. Having to tell the management, steering committee, or other decision makers that it is necessary to descope 8 security measures to avoid killing the project. I believe they will steal the focus from the 37 other security measures, the project managed to include.
I will be interesting to see, if we change that approach next year, where the NIS2 EU directive is entered into force. By then a wide list of companies that deliver services related to critical in-frastructure must comply with security measures within 10 specified categories. I checked out the directive. The categories are broad, and covers my entire brainstorm list, and additional policies and reporting procedures. Failing to comply with NIS2 can lead to large fines, and leaders can be held personal responsible. That is scary cyber security stuff.
At least I have a checklist now, and I believe that I will add more items, when they come across my mind. Separating them into categories may also help me define which security measures are relevant for which projects. Let me know what my list is missing.
1. Backup on-prem
2. Backup cloud/SaaS
3. Restore test
4. 3-2-1 backup method
5. Ransomware protection
6. Redundancy
7. DDos protection
8. Single point of failure
9. Network segregation
10. Endpoint security
11. Firewall/gateway protection
12. Break glass policies/solutions
13. IoT security
14. Segregartion of duties
15. DevSecOps
16. Secrets management
17. Sql injection protection
18. Cross site scripting
19. Brute force prevention
20. Patch management
21. Identity access management
22. Privileged access principels
23. Network Monitoring Tools (Siem)
24. Intrusion Detection Systems
25. Cloud access security broker
26. DNS filter/URL filtering.
27. Honeypot
28. Penetration testing
29. Physical access security
30. VPN when working outsite the organization’s network
31. Avoid non-company IT services
32. No non-standard software installed on personal PC’s
33. Sandboxes for testing/investigating
34. E-mail security
35. Awareness training
36. USB port policies
37. Work phone policies
38. Data categorization
39. No clear text passwords
40. Encryption in transit
41. Encryption at rest
42. Encryption key management
43. E-mail encryption
44. Disk encryption
45. Backup encryption
46. Data loss prevention solution
47. Zero-trust principle
48. Least privilege principle
49. Privileged account policies
50. Secrets management
51. RBAC
52. AD security
53. Service accounts security policies
54. Multi-factor authentication
55. Antivirus software
56. Incident response













